
TL;DR: Traditional IT support was never designed to deal with ransomware gangs, AI phishing, or supply chain attacks. Businesses that misinvest in outdated security are just as exposed as those with nothing in place. Pro-Networks' dedicated cybersecurity team and Business Armour suite exist because your security deserves the same focus as your uptime.
___________________
The cybersecurity landscape has changed beyond all recognition. The question for every business is simple: has your IT support partner kept up?
The World Your IT Support Was Built For No Longer Exists
Cast your mind back to the early days of managed IT support. The job was straightforward: keep computers running, maintain the network, patch software, respond to helpdesk tickets. Cyber threats existed, of course - viruses, the odd spam campaign - but they were manageable. A decent antivirus and a sensible firewall went a long way.
That world is gone. Today, businesses of every size are targeted by sophisticated, financially motivated criminal organisations. Ransomware gangs operate like corporations, complete with negotiation teams and customer service portals. Nation-state actors probe SME networks looking for supply chain weaknesses. AI-generated phishing emails are indistinguishable from legitimate communications. The average time to detect a breach is still measured in months, not hours - and by the time most businesses know something is wrong, the damage is already done.
Traditional IT support - reactive, ticket-driven, infrastructure-focused - was never designed to deal with any of this. And yet, millions of businesses still rely on MSPs whose security offering amounts to little more than antivirus software and a prayer.
The MSP Model Has a Blind Spot
The standard MSP model is built around availability. Keep systems up, resolve issues quickly, minimise downtime. These are genuinely valuable things, but they create a fundamental blind spot: your support team is optimised to fix problems after they happen, not to detect and prevent threats before they materialise.
Cybersecurity requires a completely different mindset. It demands continuous monitoring, proactive threat hunting, intelligence-led analysis, and rapid incident response. These are not helpdesk skills. They require dedicated security professionals with specialist training, access to threat intelligence feeds, and the tools to correlate events across an entire environment in real time.
An MSP that hasn't built a dedicated security capability isn't just falling short - it's actively creating a false sense of security. Customers believe they're protected. They're not.
This is the uncomfortable truth facing the MSP industry: the businesses that helped organisations adopt technology over the past two decades now need to fundamentally evolve their offering, or accept that they are leaving their customers dangerously exposed to modern threats.
What a Modern Cyber Threat Landscape Actually Looks Like
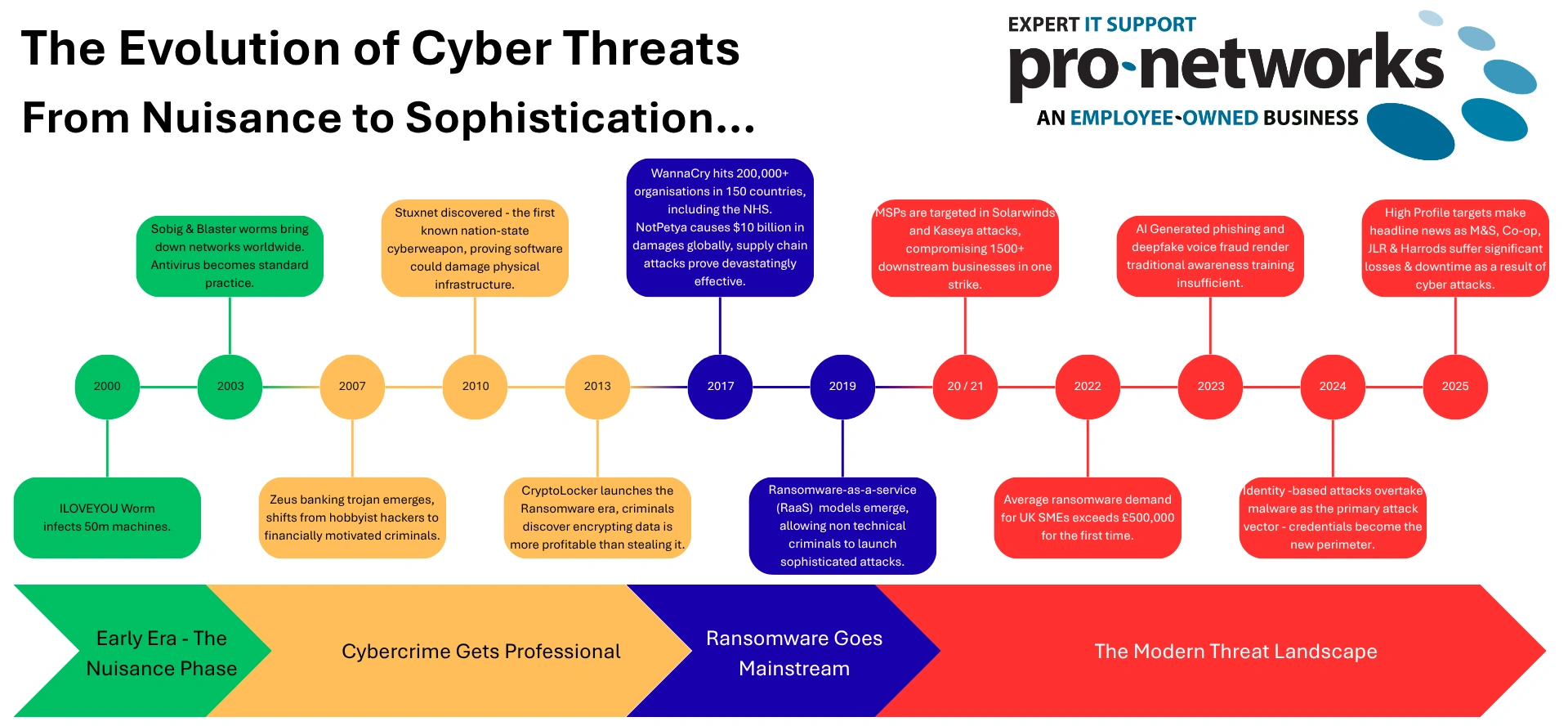
To understand why the evolution from MSP to MSSP matters, it helps to be specific about what businesses are facing right now, but before we do this - let's review how the threat has evolved since the year 2000…
Ransomware remains the defining threat for SMEs. Attacks are increasingly targeted rather than opportunistic - criminals research their victims, identify key systems, and time attacks for maximum disruption. The average ransom demand for UK SMEs now runs into tens of thousands of pounds, before you factor in downtime, recovery costs, reputational damage, and regulatory scrutiny.
Business Email Compromise (BEC) is quietly becoming just as damaging. Attackers compromise email accounts, monitor correspondence, and then intercept financial transactions at precisely the right moment. No malware is involved. Traditional security tools often see nothing unusual until it's too late.
Supply chain attacks have moved from the realm of nation-state espionage into everyday criminal activity. Your business doesn't need to be the primary target - it just needs to be connected to one. MSPs themselves have historically been attractive targets precisely because compromising a single provider gives attackers access to dozens of client environments simultaneously.
And underpinning all of it is the human element. The vast majority of successful attacks begin with a person - clicking a link, reusing a password, being deceived by a convincing impersonation. Technology alone cannot solve this. Security awareness, ongoing education, and a culture of vigilance are just as important as the tools you deploy.
The MSSP Difference: Proactive, Dedicated, Always On
A Managed Security Services Provider (MSSP) doesn't just support your technology - it actively defends your business. The distinction might sound subtle, but in practice it is the difference between having a smoke alarm and having a fire brigade.
Where an MSP responds to incidents, an MSSP works to prevent them. Where an MSP monitors your systems for performance, an MSSP monitors for threats. Where an MSP's security knowledge sits alongside a dozen other specialities, an MSSP's entire focus is on keeping your business safe.
Critically, this requires separation. The team responding to helpdesk tickets cannot also be responsible for threat detection and incident response - not because of capability, but because of capacity and focus. Security operations require dedicated attention, specialist tooling, and the mental bandwidth to think like an attacker. That cannot be bolted onto a busy support function as an afterthought.
How Pro-Networks Has Evolved - and Why It Matters to You
At Pro-Networks, we recognised this shift early. We made the decision to invest in a dedicated cybersecurity team that operates entirely separately from our IT support function. Not the same engineers wearing two hats. Not a security checklist added to the support workflow. A genuine, independent security capability focused exclusively on protecting our clients.
This team is the engine behind Business Armour - our suite of cybersecurity solutions built specifically for the threat landscape SMEs and mid-market businesses face today. Business Armour isn't a single product — it's a layered, intelligence-led approach to security that spans prevention, detection, and response.
What that means in practice:
- Continuous monitoring of your environment, 24 hours a day, 7 days a week — not just during business hours
- Proactive threat hunting that looks for the indicators of compromise before an attack completes
- Advanced endpoint detection and response (MDR) that goes far beyond traditional antivirus
- Email security (ITDR) and anti-phishing protection designed to catch the sophisticated attacks that bypass standard filters
- Security awareness training and phishing simulations that turn your people from a vulnerability into a line of defence
- Incident response planning and support, so that if the worst happens, you know exactly what to do — and we're ready to help
The fact that this sits outside of our support function is a deliberate and important design choice. Your helpdesk experience isn't compromised by security demands competing for the same team's attention. And your security isn't compromised by being treated as a secondary concern. Both functions operate at full capacity, in parallel, for your benefit.
The Question Every Business Should Ask Its IT Provider
If you're currently working with an MSP — whether that's us or someone else — there are questions worth asking. Not to catch anyone out, but because the answers genuinely matter to your resilience as a business.
- Does your IT provider have a dedicated security team, separate from support?
- Do they monitor, and act on, your environment outside business hours?
- Can they demonstrate how they would detect a threat that doesn't trigger a traditional alert — a slow credential theft, a dormant piece of malware, a compromised but legitimate account?
- What is their incident response capability, and have they tested it recently?
- Can they evidence ongoing investment in security expertise and tooling?
If the answers are vague, or if security is described as something that happens alongside support rather than independently of it, that is a conversation worth having - and a gap worth taking seriously.
The Stakes Are Too High to Stand Still
Having a security budget doesn't make you safe. Businesses that invest in the wrong solutions - tools built for yesterday's threats, managed by teams without dedicated security expertise - are just as vulnerable as those who never invested at all. The only difference is they don't know it yet.
The evolution from MSP to MSSP isn't an upgrade. It's a necessity. The threat landscape has moved, and businesses need partners who have moved with it.
Pro-Networks has made that move. Business Armour and our dedicated cybersecurity team exist because we believe our clients deserve a partner that takes their security as seriously as their uptime - and has built a team and a suite of tools to prove it.
If you'd like to understand how Business Armour could strengthen your defences, we'd welcome the conversation. Because in cybersecurity, the time to act is always before an incident - never after.
