
Your Security Stack Has Gaps You Can't See
The case for a centralised SIEM — even when you already have ITDR and MDR
TL;DR
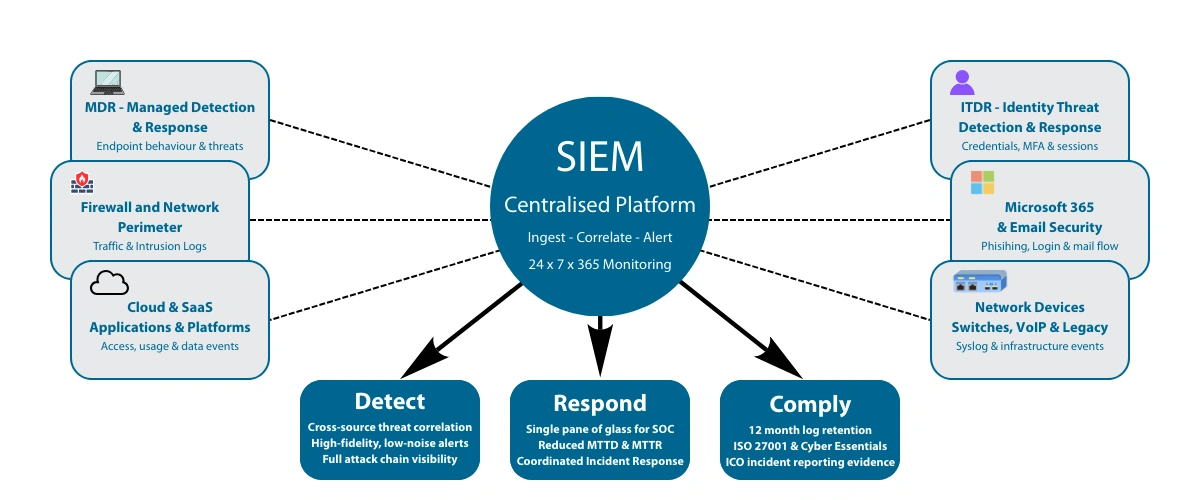
MDR protects your endpoints. ITDR protects your identities. But when attackers move across multiple systems — using your firewall, your cloud apps, your network — no single tool sees the full picture. A centralised SIEM ingests logs from every source and correlates them, turning scattered low-level alerts into one clear, high-confidence view of what's happening across your entire environment. It also satisfies the long-term log retention requirements that compliance frameworks like ISO 27001 and Cyber Essentials Plus demand. If you already have MDR and ITDR, a SIEM is what ties them together.
| Security Tool | What it Monitors | Purpose |
| MDR | Endpoints (laptops, servers) | Detect and contain malware and endpoint attacks |
| ITDR | Identity systems (Entra ID, AD) | Detect credential abuse and identity compromise |
| SIEM | Entire environment | Correlate logs across systems to detect complex attacks |
______________________
Your Security Stack Has Gaps You Can't See
The case for a centralised SIEM — even when you already have ITDR and MDR
If your business has invested in MDR and ITDR, you're ahead of most. You may have:
- MDR (Managed Detection and Response) to spot and contain endpoint threats
- ITDR (Identity Threat Detection and Response) to stop credential misuse, privilege abuse and identity-based attacks
For many businesses, that feels comprehensive — two strong tools watching two critical areas.
But there's a question that often gets missed: if each tool is watching its own part of your environment, who's watching the whole thing?
A centralised Security Information and Event Management (SIEM) platform fills that gap. It's not just another tool — it's the intelligence layer that makes your existing security controls work together.
A sophisticated attacker rarely sets off a single alarm. They leave clues across multiple systems — and without a SIEM, nobody connects the dots.
What MDR and ITDR do brilliantly — and where they stop
MDR: Endpoint visibility
MDR monitors laptops, desktops and servers in real time. It detects suspicious behaviour — including "living off the land" attacks that avoid traditional antivirus — and can isolate a compromised device before an attacker moves deeper. Our MDR service runs 24×7×365, giving you SOC-grade monitoring without building a SOC yourself.
ITDR: Identity visibility
ITDR focuses on identity systems: Microsoft Entra ID, Active Directory, authentication flows, privilege escalation, and session activity. It detects identity-based attacks that MFA alone cannot stop — including session token theft, where attackers bypass authentication entirely.
Both are powerful. Both provide alerts. But they only see their own slice of your environment. That's the limitation.
The problem with siloed detection
Modern cyberattacks are multi-stage. For example:
- A VPN connection from an unusual region (firewall log)
- A successful login using stolen credentials (identity log)
- Lateral movement using legitimate admin tools (network log)
- Data exfiltration through a trusted cloud app (SaaS log)
Individually? Low-priority. Together? A clear breach in progress.
A SIEM ingests all these logs and correlates them. Instead of several low-value alerts scattered across different dashboards, you get:
One high-confidence, cross-system alert showing the full attack chain.
That's the power of context — and only a SIEM provides it.
What a centralised SIEM adds to your security stack
1. Full-environment visibility
MDR sees endpoints. ITDR sees identities. But what about firewalls, switches, legacy servers, VoIP systems, SaaS platforms and cloud workloads? A SIEM can ingest logs from almost any device or service via syslog, API or log forwarding — filling the visibility gaps your other tools don't cover.
2. Cross-source correlation
This is the SIEM's real superpower: connecting dots across disparate systems to tell the story of an attack. Correlation supports threat hunting, incident investigation, multi-stage attack detection and a significant reduction in alert fatigue. Without it, analysts juggle dashboards and manually piece together events — and attackers rely on that gap.
3. Compliance and audit readiness
Across the UK and internationally, security regulations are tightening. Frameworks such as ISO 27001, Cyber Essentials Plus, PCI DSS and the UK Cyber Security and Resilience Bill require long-term log retention, monitoring, and the ability to evidence activity — often going back 12 months or more. A SIEM becomes your tamper-evident system of record, making audits faster, cleaner and less stressful.
4. Faster detection and faster response (MTTD & MTTR)
Two metrics define how effectively you stop threats:
- MTTD (Mean Time to Detect) — how long from the start of suspicious activity until your systems notice it.
- MTTR (Mean Time to Respond) — how long from detection to full remediation: isolating hosts, stopping the attacker and restoring operations.
Every minute matters. Attackers don't wait — they escalate privileges, spread, and exfiltrate. A SIEM, especially when monitored 24×7 by a SOC, significantly reduces both MTTD and MTTR by surfacing fewer, higher-fidelity alerts with the complete attack context already assembled.
Who benefits most from a centralised SIEM?
Although almost every organisation gains value, the strongest use cases are:
- Compliance-driven sectors needing long-term audit logs
- Hybrid environments (on-prem + Microsoft 365 + SaaS + cloud platforms)
- Businesses that have experienced incidents and want better forensics next time
- Organisations already using MDR and ITDR that want correlation across both
- Growing SMEs and mid-market companies with expanding attack surfaces
If you already have MDR and ITDR, you've made the right investments. A SIEM ties those investments together — the senior investigator who reads every report and sees the bigger picture.
How Pro-Networks approaches SIEM
Our centralised SIEM platform is part of our Business Armour cybersecurity suite. It's designed to work with your MDR and ITDR tools, not replace them. We handle deployment and configuration, log onboarding and tuning, correlation rule development, 24 × 7 x 265 monitoring, investigation and response, and reporting and compliance support.
You get enterprise-grade visibility and intelligence — without hiring a dedicated SOC.
If you're already running MDR, ITDR or both and want to understand what a centralised SIEM would add to your specific environment, get in touch for a no-obligation conversation about your current setup.
